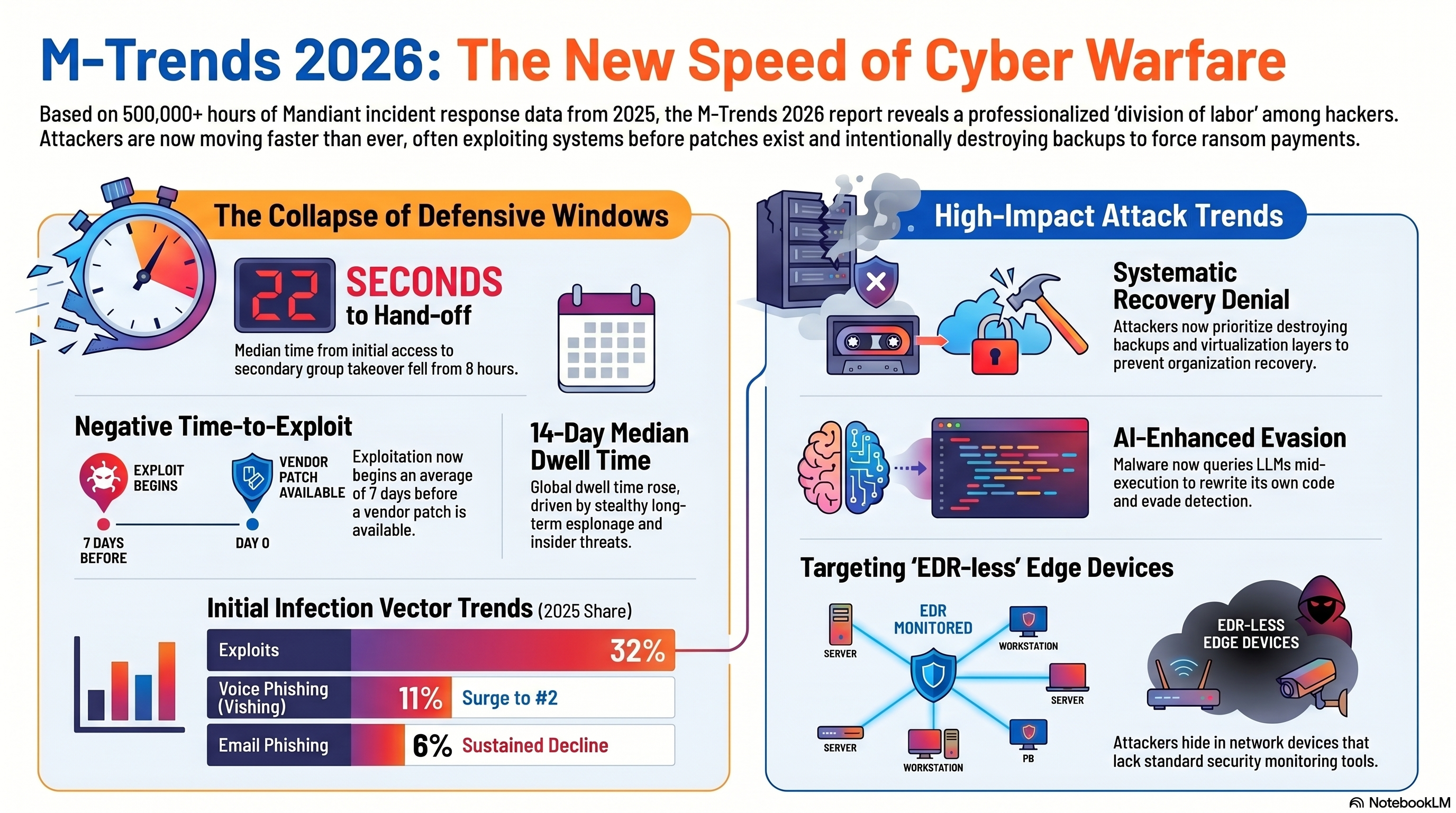
22 seconds. That's all it takes in 2026 from the moment an attacker enters a network — until they hand over access to a ransomware gang.
This week, let's step back from individual stories and look at the big picture. Mandiant (Google's cyber intelligence firm) has released the M-Trends 2026 report — based on half a million hours of real-world incident investigations. And the numbers? They're chilling.
The Number That Says It All: 22 Seconds
In 2022, when an attacker breached a network, it took them an average of 8 hours to hand over access to another player (ransomware gang, state actor, etc.). In 2025? 22 seconds.
You read that right. Less time than it takes to make a cup of coffee. The attacker enters, transfers access, and someone else is already deploying ransomware — before the SOC analyst has even finished reading the alert.
This means crime has evolved from a "lone hacker" into an industrial assembly line — where everyone specializes in their specific stage.
How do they get in? The 2025 numbers
- 🔸 32% — Exploiting vulnerabilities — Still #1, for the sixth year in a row.
- 🔸 11% — Voice Phishing (Vishing) — Jumped to second place. Attackers are calling over the phone and impersonating IT.
- 🔸 14% — Stolen credentials — Leaked passwords, infostealers, dark web.
- 🔸 8% — Email Phishing — It's down. Not because it doesn't work, but because vishing works better.
The Most Alarming Stat: Negative Exploit Time
The average time from when a vulnerability is published until attackers exploit it: minus 7 days. Yes, minus. This means that in 28.3% of cases, attackers exploited the vulnerability before the patch was even released. In 2020, it took 700 days to develop an exploit. In 2025 — 44 days. And the trend continues.
What attackers do after they're in
- 🔴 Destroying backups first — Ransomware in 2025 focuses first on vSphere, ESXi, and backups. They delete the safety net before encrypting.
- 🔴 Living off the Land — Using legitimate tools already present in the system (PowerShell, WMI, RDP) to move through the network without triggering alerts.
- 🔴 Attacking Cloud Infrastructure — Moving from on-prem to the cloud via trust relationships, service accounts with excessive permissions, and non-expiring API tokens.
- 🔴 714 new malware families — Up from 632 the previous year. Total? Over 6,000 documented malware families.
And where does AI fit in?
- 🔸 Mandiant documented malware using LLMs during runtime — asking the AI how to evade detection and changing its code accordingly.
- 🔸 Google exposed PROMPTFLUX — malware that uses the Gemini API to rewrite its own source code with every execution. There is no fixed signature — every version is different.
- 🔸 AI tools have cut exploit development time from days to hours.
- 🔸 AI Voice Phishing generates phone calls that sound exactly like a coworker or an IT person.
But — and this is important — Mandiant states that as of today, AI is still an accelerator of existing techniques, not a new revolution. What kills organizations in 2025 is still the basics: unpatched vulnerabilities, weak passwords, non-segregated backups, and unaware employees.
The Good News
- ✅ 52% of breaches in 2025 were identified internally by the organization itself — up from 43% in 2024. Organizations are getting better at detection.
- ✅ Median Dwell Time — how long an attacker stays in the network before being discovered — dropped to 10 days for internal detection. A decade ago, it was months.
The Bottom Line
The race in 2026 is clear: attackers exploit vulnerabilities within hours, transfer access within seconds, and destroy backups before encrypting. AI accelerates everything — on both sides.
The organizations that survive aren't the ones with the most expensive tools — they are the ones managing the basics correctly: fast patching, MFA everywhere, segregated backups, minimal permissions, and employees who know how to identify a suspicious phone call.
The numbers don't lie. 22 seconds is all you have.